How To Run The Bitaddress.org Tool In A Secure Offline TAILS Temporary Live Boot Session

Introduction
This article assumes that you have completed the previous guide on setting up an TAILS temporary live boot session. The task for this article is to safely download The Bitaddress.org Tool directly from GitHub so we can run it from the local machine while it is disconnected from the internet.

It is important we go through these set of steps rather than using the tool via the web. This is in order to keep your private keys somewhat in a state of cold storage where they don't touch a machine that is connected to the internet. We will not use Google or other service (that may be tracking you) to download the tool. Instead, we will download it directly from its source.
If you are using this tool to access your private key, the components will not be typed into this machine until it has been disconnected from the internet. Since by design, the TAILS OS will not write anything to the hard drive, it will not retain any memory of the keys. It is unlikley that this method is defeated highly-sophisticated malware that evades these precautions, but not impossible. By running offline, at the very least, you can power-cycle to erase all traces of the session before reconnecting to the internet.
Download The Bitaddress.org Tool From Github
Git is installed by default on TAILS. The first step here is to use Git from the Terminal application to clone the bitaddress.org repository https://github.com/pointbiz/bitaddress.org from GitHub onto the local machine.
This can be done by opening the Terminal app via the Applications menu entry and typing into the terminal:
git clone https://github.com/pointbiz/bitaddress.org
Then and press Enter. It will take a couple seconds look like this when it is done:
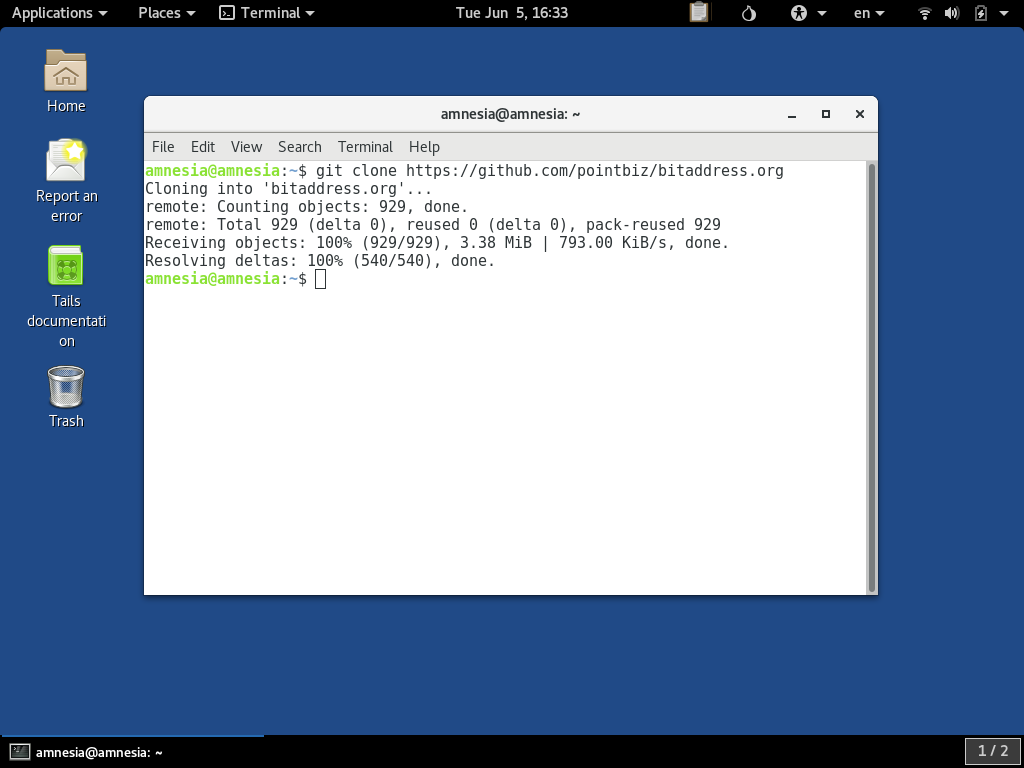
This downloads the source code provided into the amnesia user's home directory. Since this is a temporary live boot session, this is not actually written to any disk, but rather just held in the computer's RAM for the remainder of the time the PC is powered on. However, it does function as if it were on a hard drive as far as the software can tell.
If you access the tool via the web at bitaddress.org, it redirects to a URL https://www.bitaddress.org/bitaddress.org-v3.3.0-SHA256-dec17c07685e1870960903d8f58090475b25af946fe95a734f88408cef4aa194.html. As you can see it has the Sha256 checksum dec17c07685e1870960903d8f58090475b25af946fe95a734f88408cef4aa194 as a component. To be absolutely sure we got the right software, we can check that the file we downloaded exactly matches this checksum value.
This can be done by typing the command:
sha256sum bitaddress.org/bitaddress.org.html
Then pressing Enter like so:
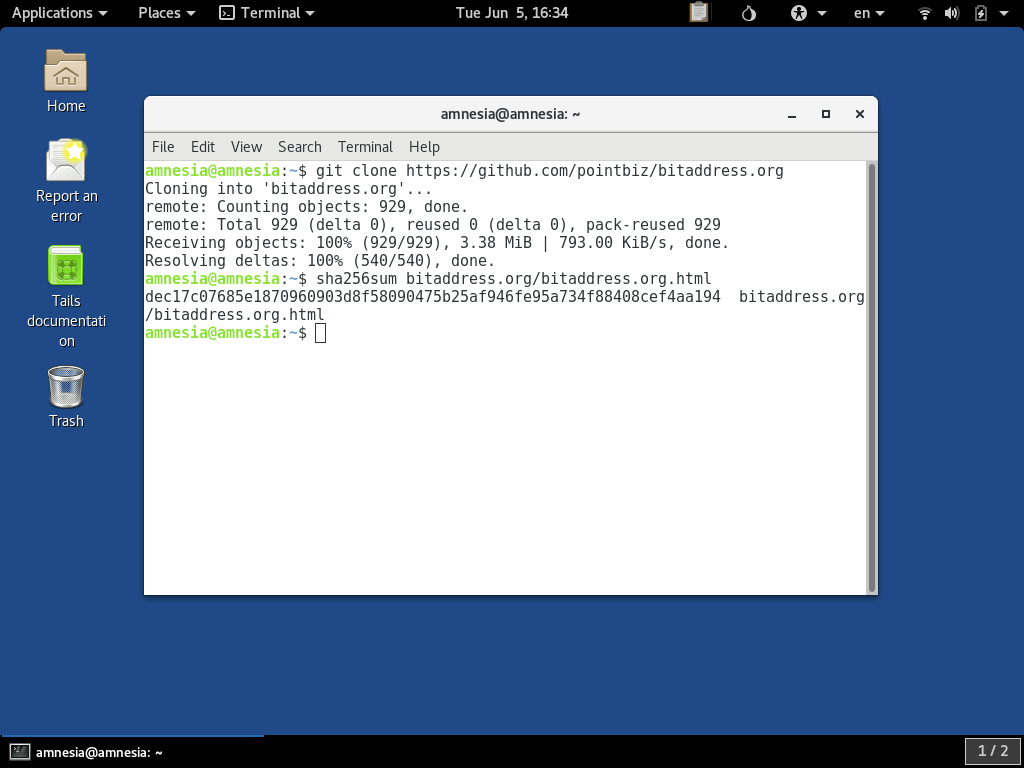
This uses TAILS's built-in utility sha256sum to checksum the file which git downloaded to the bitaddress.org/ directory as a file named bitaddress.org.html. You should get the exact answer dec17c07685e1870960903d8f58090475b25af946fe95a734f88408cef4aa194, which is impossible to forge with a different file as long as the sha256 hash algorithm remains secure.
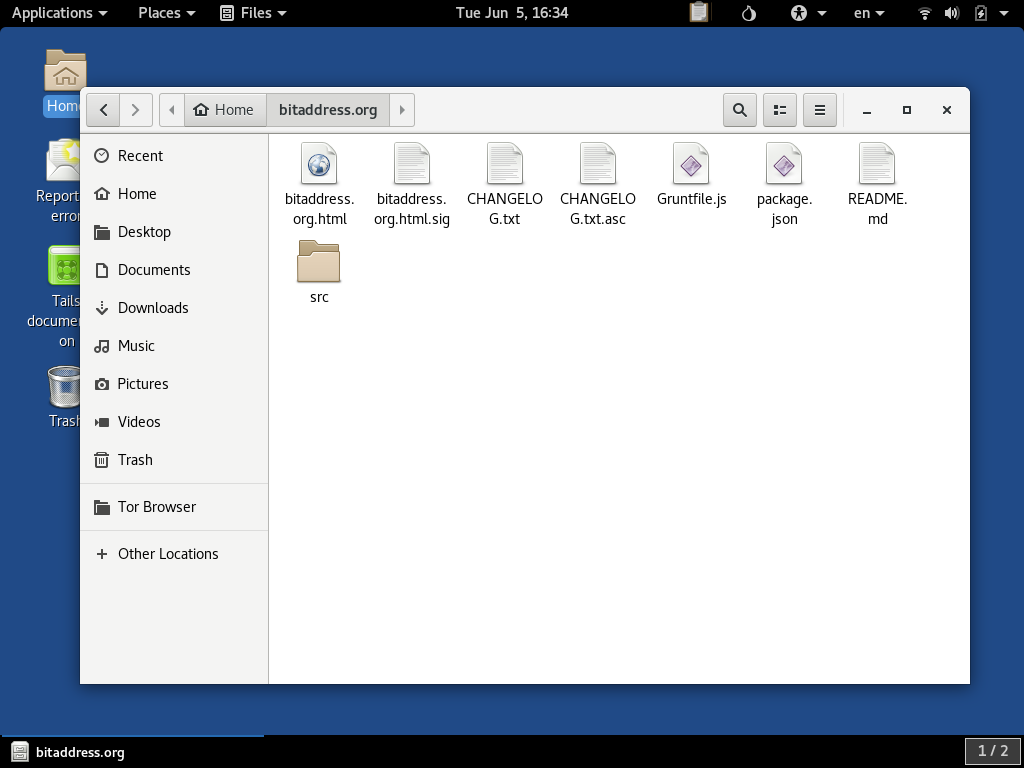
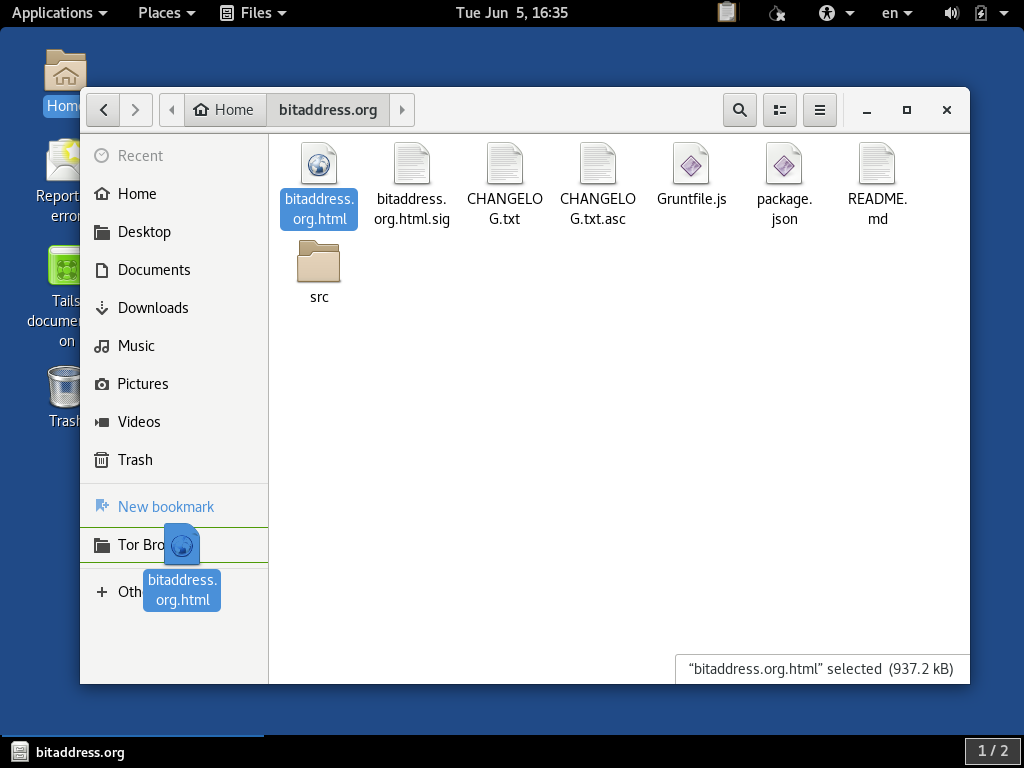
We can now close the Terminal window, and open TAILS's GUI file explorer tool by double-clicking on the Home folder icon on the desktop. In the window that comes up, you should see a folder called bitaddress.org which is the first item in the user's home folder. If you double-click on it, the file explorer shows the contents of the folder which should look like this:
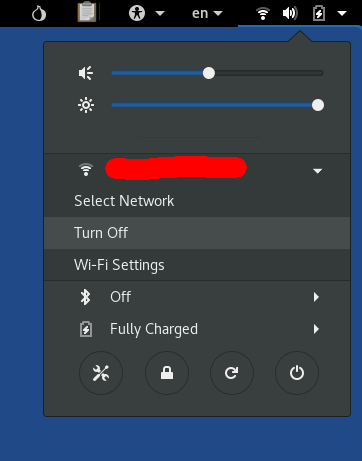
Disconnect From the Internet
Before we run the tool, we should disconnect from the internet. TAILS's network control menu is in the top right corner. Networking can be disabled. Additionally, to be completely sure you are offline, you can consider unplugging your computer's Ethernet cable (if it is connected that way) or switching off any hardware networking disabling switches if, for example, you have one on the laptop you are using. What you see in the menu will vary depending on your network hardware, but this is what the menu looks like:
Open The Bitaddress.org Tool With Tor Browser
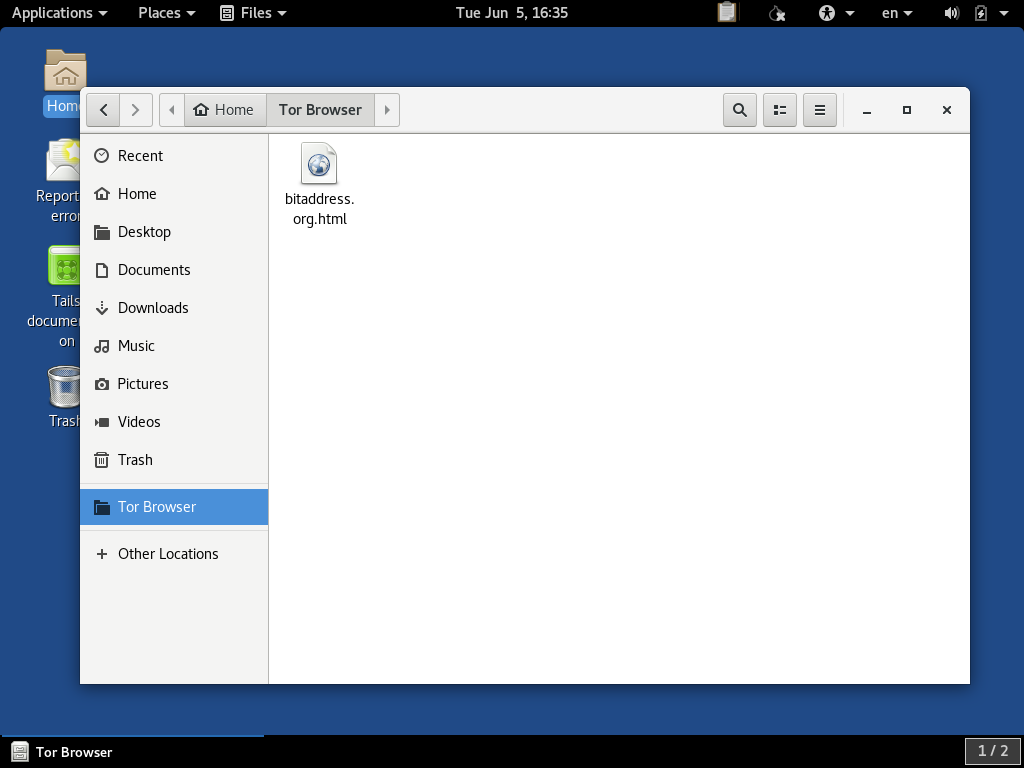
One common source of confusion on TAILS is that the Tor Browser is locked down to only allow it to access files under the Tor Browser directory. To open this standalone HTML file, we need to copy it into this directory. We do so by dragging it to the Tor Browser folder on the sidebar of the file browser view:
We can then double-click on the same Tor Browser folder to open it:
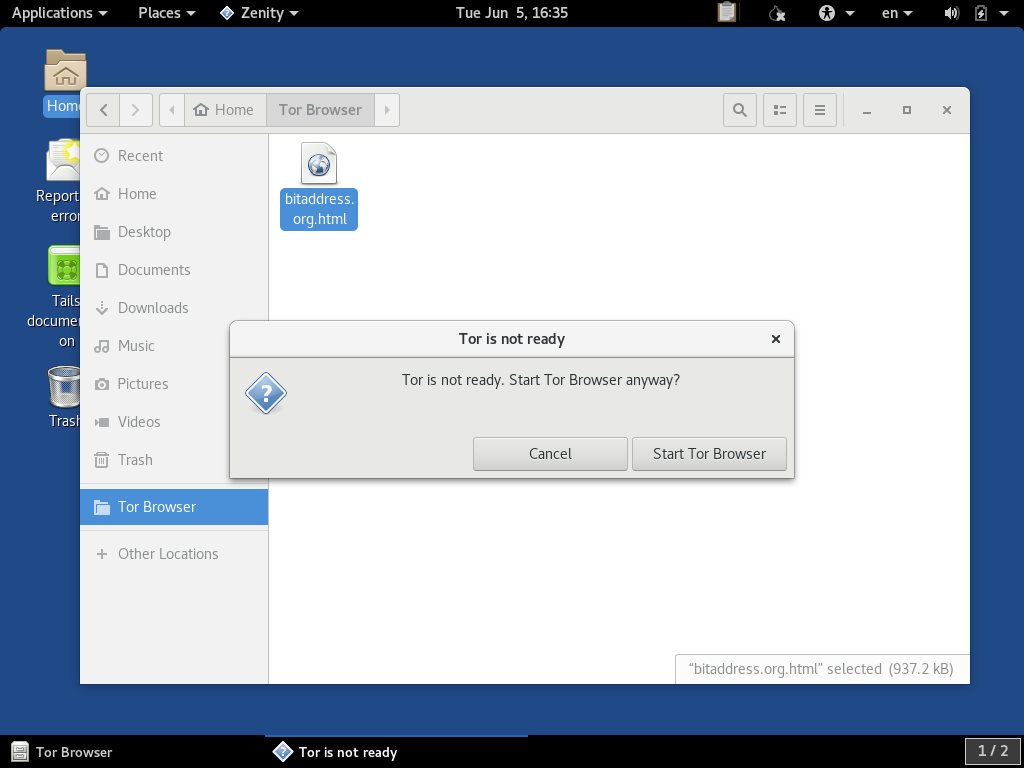
If we double-click the HTML file, you should get prompted to tell you that you are trying to open Tor Browser without being connected to Tor because you are currently offline. This is exactly what we are trying to do, and you can select starting Tor Browser anyway:
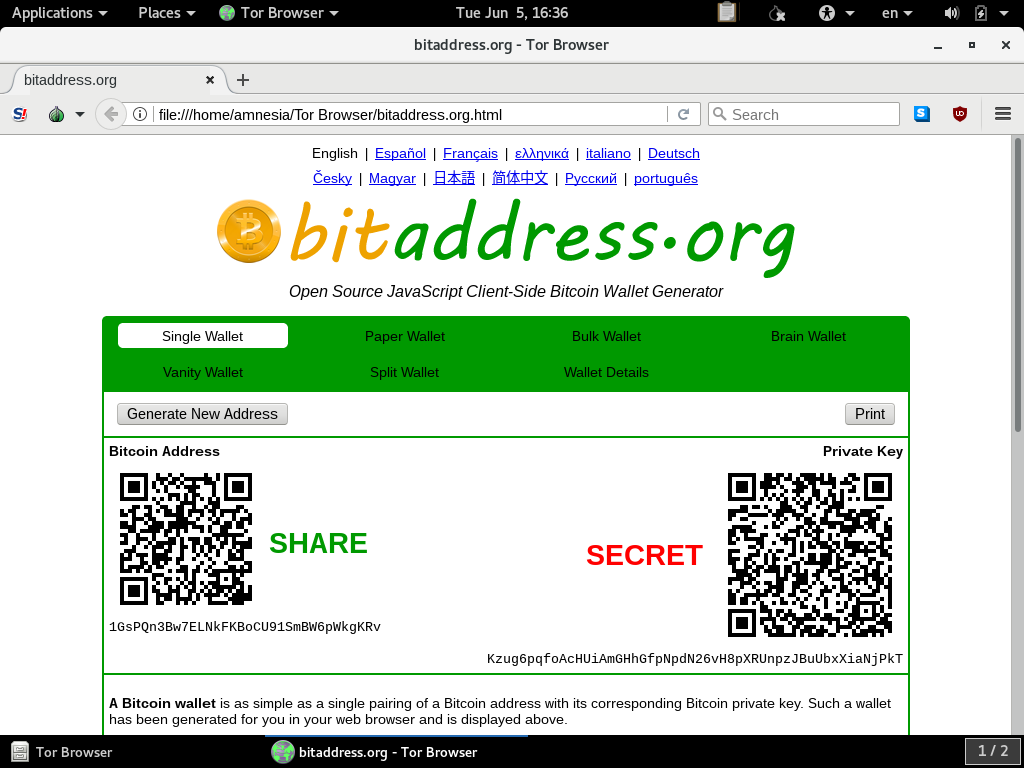
When the Bitaddress.org tool is opened, it should look like this:
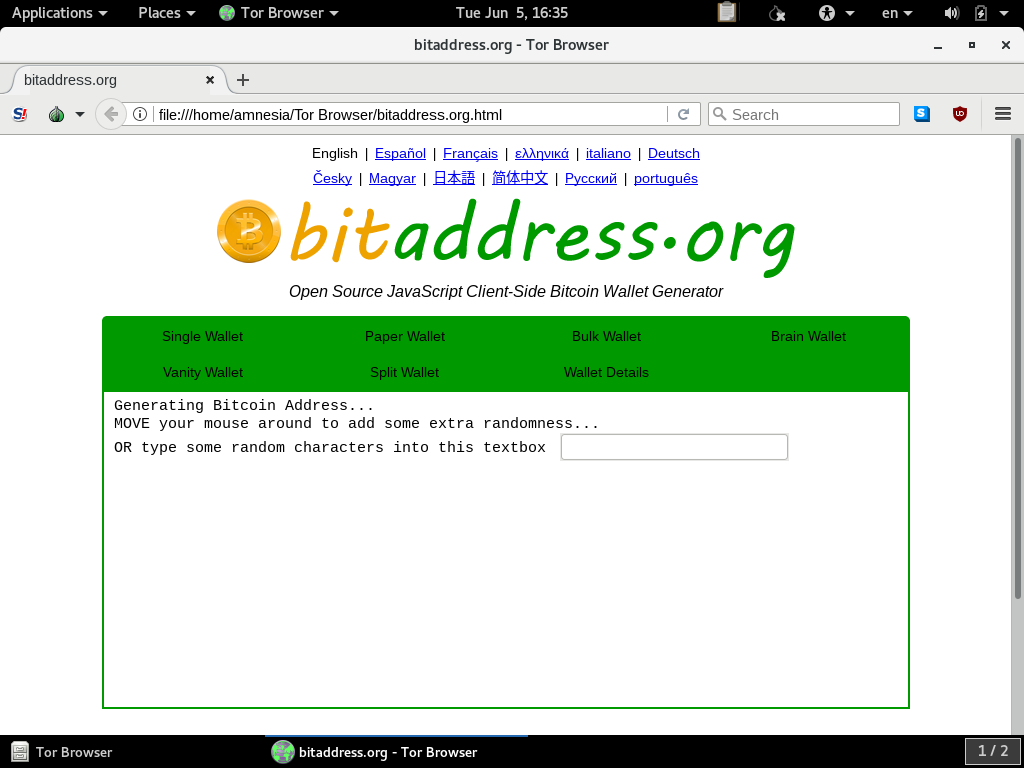
This tool can now be used to generate private keys or type in and operate on BIP38 encrypted private keys or split wallet fragments.
If, for example, you are using the bitaddress.org took to generate paper wallets to print, TAILS may or may not have sufficient drivers for USB printers that can be used while this machine is offline. If this turns out to be a barrier to printing, the BIP38-encrypted printouts might be able to be printed from an offline Ubuntu temporary live session which likely has better printer driver support built in.
When you are finished with using this tool, you can close the Tor Browser window, and shut down the PC. It will not retain any memory of what was done during this session.